Police officials say hacking the phone of Andrea Farrington, who was shot and killed last summer at the Coral Ridge Mall, is too risky to justify, even after the FBI unlocked the phone of a participant in the San Bernardino, California, terrorist attack.
The homicide trial will begin Tuesday for Alexander Kozak, who is charged with killing Farrington. The trial will likely last two weeks.
The U.S. criminal-justice system is now facing hard questions on privacy and technology use after the phone of Syed Rizwan Farook — who participated in the San Bernardino terrorist attack, which left 14 people dead — was unlocked by the federal agency.
“In our last cell-phone case, we sent it to who was supposed to be the premier expert in the country, and he couldn’t unlock it,” Lt. Shan Kron of the Coralville police said.
He said evidence of a crime can be lost, and it isn’t uncommon for evidence from computers and phones to be disregarded in fear of losing the evidence altogether.
“It’s kind of all or nothing,” he said. “You can’t risk damaging evidence, so that’s where we stopped on the case.”
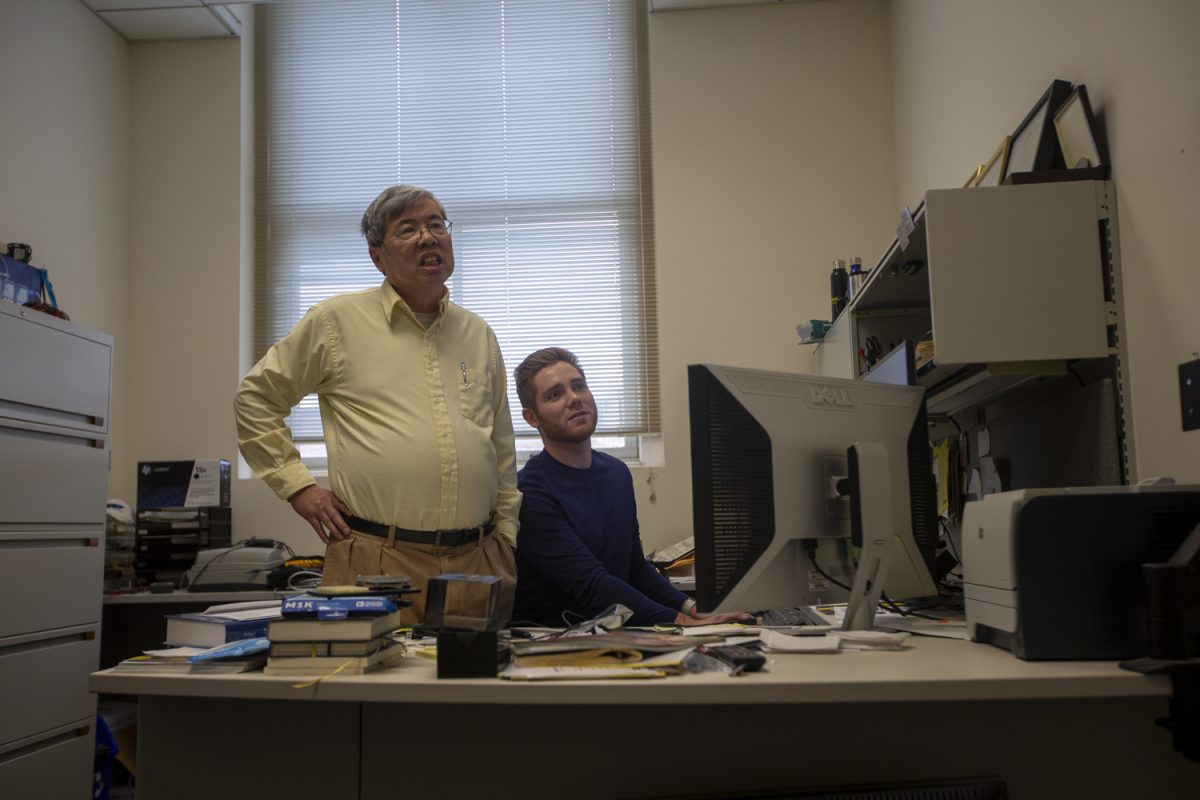
Todd Cheney, an Iowa City computer forensics officer, said phone systems are changing faster than ever, and it has become very difficult for agencies to keep up with the security programs companies produce.
“There are so many factors that when people come in and ask whether I can get into a phone, I’d have to know what make it is, what model it is, and what version the IOS or Android is on,” he said. “It used to be you could brute force attack them, which means you could keep trying different combinations until you found the one that unlocks it.
“Apple has since secured its phones by adding an automatic wipe after 10 failed attempts. That basically eliminates us being able to try that.”
The FBI’s equipment is likely no different from ones used in local investigations, Cheney said, but the resources available to the FBI may allow for more time and a more recent update needed for a particular device.
For law enforcement, this means investigators risk letting criminals go in a trial in order to preserve evidence that might be able to be solved in the future.
Kron said DNA evidence was once thought to be useless in investigating crimes, but now, with current technology, crimes from 30 years ago are being solved.
“That’s the risk in destroying evidence. It’s almost a no-win, you don’t get the information off of it, but yet it’s still there,” he said. “The implication [in trial] is there was something you didn’t want people to see and you destroyed it, whether you sent it to the expert, it doesn’t matter. The implication is you buried it because you didn’t want people to see it.”
With new phones and systems coming out quicker then ever, law-enforcement officers try to keep up with program updates. Kron said what was once an update every six months to a year has become a constant endeavor.
In response to the FBI dropping the case filed after a suit was filed, Apple said in a press release that the hacking of private cell phones raises various privacy concerns.
“From the beginning, we objected to the FBI’s demand that Apple build a back door into the iPhone because we believed it was wrong and would set a dangerous precedent,” the statement said.